by Megan Daudelin
September 17, 2015
Log monitoring is a daunting task that many organizations have difficulty tackling efficiently. For most organizations, the rate of log generation far exceeds the ability to of a security team adequately monitor it. Quickly identifying events of value through the noise is crucial to maintaining the security of a network. By leveraging the capabilities of SecurityCenter and the Log Correlation Engine (LCE), security teams can identify possible security breaches more efficiently.
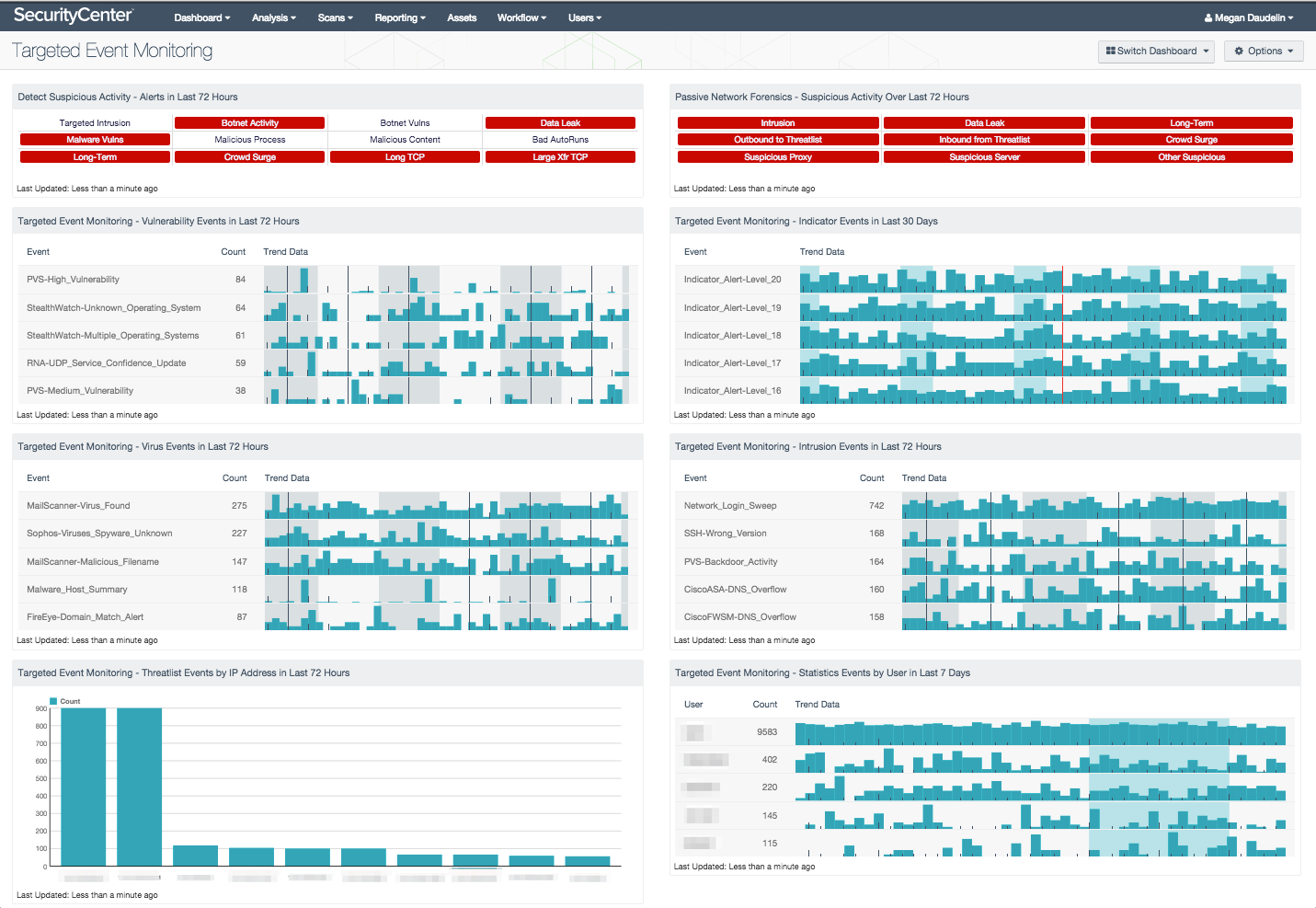
The Targeted Event Monitoring dashboard assists security teams in identifying important events in their logs so that faster remediation is possible. The dashboard relies on normalized logs from LCE, which provides a tailored view of the events on the network related to potential security concerns. Events are filtered by type, IP address, and user in order to provide the most accurate view of potential security issues. This dashboard cuts through the gigabytes of logs and focuses on events closely related to the security of a network.
The components in this dashboard provide several views into the security status of the network to help security teams monitor important events generated from log analysis and ensure that necessary remediation or hardening measures can be implemented. Several components are focused to the past three days of activity in order to focus on the most current events that may need remediation, while others provide a lengthier trend of events over the past seven or thirty days. Tables are filtered by crucial event types to enable monitoring and timely remediation. Analysts are alerted to suspicious activity that has been detected in the past three days and can review the events that triggered these alerts. Together, the components in this dashboard provide a platform from which analysts can efficiently monitor logs for events crucial to network security.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.2
- LCE 4.6.0
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. The Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with LCE, SecurityCenter CV provides the most comprehensive view of network security data.
This dashboard includes the following components:
- Detect Suspicious Activity - Alerts in Last 72 Hours: This matrix presents warning indicators for potentially suspicious network activity detected in the last 72 hours, such as targeted intrusions (intrusion attacks that targeted systems and ports likely to be exploited by the attacks), botnet activity, and long-term activity. Each indicator is based either on one or more Log Correlation Engine (LCE) events, or on active or passive vulnerability detections; the indicator is highlighted red if the event occurred in the last 72 hours. Any warnings should be further investigated. More information can be obtained on these events (such as details, time, and IP address) by clicking on the specific indicator and viewing the raw syslog (for events) or the detailed vulnerability list (for vulnerabilities).
- Passive Network Forensics - Suspicious Activity Over Last 72 Hours: This matrix presents indicators of suspicious events that have occurred in the last 72 hours, including intrusions, potential data leaks, potentially unwanted long-term activity, threatlist activity (interaction with known botnets), crowd surges, suspicious proxy activity, suspicious server activity, and other suspicious host activity. Clicking on a highlighted indicator will bring up the analysis screen to display details and allow further investigation. Note that this component relies on PVS detections being forwarded via syslog to the LCE.
- Targeted Event Monitoring - Vulnerability Events in Last 72 Hours: The Vulnerability Events in Last 72 Hours table displays the vulnerability events by count detected in the last three days. Events are normalized by LCE and filtered on the event type "vulnerability," which includes security issues and new information about systems and networks that are reported as part of the vulnerability monitoring process. This component alerts analysts to the most prolific vulnerability events detected recently so that mitigation, containment, or realignment measures can be taken. Events are generated by a variety of devices and can serve as a starting point for focusing hardening processes.
- Targeted Event Monitoring - Virus Events in Last 72 Hours: The Virus Events in Last 72 Hours table lists the virus events by count detected in the last three days. Events are normalized by LCE and filtered on the event type "virus," which can include logs that indicate the presence of a virus in email, a virus found on a system by antivirus software, or virus logs found by network IDS events and firewalls. This component alerts analysts to possible malware infections seen in the past three days to enable quick remediation. Directing focus toward the most recent and prolific infections helps reduce the time between discovery and containment.
- Targeted Event Monitoring - Intrusion Events in Last 72 Hours: The Intrusion Events in Last 72 Hours table displays the intrusion events by count detected in the last three days. Events are normalized by LCE and filtered on the event type "intrusion," which denotes logs from network IDS, firewalls, applications, and operating systems that indicate some sort of network attack. This component alerts analysts to recent potential intrusion attempts to allow for remediation or reconfiguration.
- Targeted Event Monitoring - Indicator Events in Last 30 Days: The Indicator Events in Last 30 Days table displays the trend of indicator events sorted by alert level over the past month. Events are normalized by LCE and filtered on the event type "indicator," which monitors events associated with scanning, compromises, anomalies, and other behaviors indicative of determined attackers or advanced malware. Any IP address that has had at least two unique events occurring in a short period of time is assigned an alert level and monitored. The alert level for an IP address is increased on a scale of 1 to 20 for each new event detected. The trend data shows analysts patterns within the events at each level and can be used to identify anomalous alerts. This component assists analysts in determining whether intrusion or infection attempts are successful so that remediation measures can be taken.
- Targeted Event Monitoring - Threatlist Events by IP Address in Last 72 Hours: The Threatlist Events by IP Address in Last 72 Hours bar chart displays the IP addresses with the highest counts of threatlist events. Normalized events from LCE are filtered for the event type "threatlist," which is assigned when LCE detects a connection between an internal IP address and a hostile external IP address. LCE maintains a list of hostile IP addresses that are known to be involved in botnets. This component shows the IP addresses that have the most connections to a hostile IP address during the past three days, which could be an indication of malicious activity. The IP addresses identified may need additional hardening, reconfiguration of software, or monitoring of activity.
- Targeted Event Monitoring - Statistics Events by User in Last 7 Days: The Statistics Events by User in Last 7 Days table lists the users associated with the highest counts of statistics events. Results are normalized by LCE and filtered by the event type "stats." Events of this type are created when a statistical deviation is detected for any event. This component shows which users have generated the most events in the past week as well as the trend of events over that time. Analysts can use this table to identify unusual activity from a particular user so that remediation or hardening measures can be implemented.