by Josef Weiss
October 16, 2014
Organizations often express difficulty in identifying devices on the network or software installed on systems. This report displays triggered detections within the environment, using active, passive and event based detection methods. When the organization stays up-to-date on the state of the environment, they are able to maintain a successful security program. As information about new vulnerabilities are discovered and released into the general public domain, Tenable’s research staff designs plugins to detect them. This dashboard collection utilizes both active and passive detection plugins, filtered by plugin family, to present data to the analyst. Not all detection plugins are indications of severe vulnerabilities. Many plugins are informational-based, thus provide indicators and tables of triggered detections within the environment.
Examples of the informational indicators are:
- VMware Virtual Machines
- Telnet Servers
- VNC Software
- Dropbox Software
- iCloud, and many more.
By reviewing this report, analysts can maintain an awareness of the systems and software detected within the environment. The report includes trend components that display active and passive detections over the previous 25-day reporting period. The graph typically alerts high with activity spikes for active detections on days that Nessus scanning has occurred, which alerts the analyst when active scanning is taking place. There are two indicator components for active and passive detection by plugin family and a table that displays the top 50 most prevalent detections. A severity table is provided to quickly allow the analyst to determine the physical counts of detections by severity and if any of the detections are exploitable.
SecurityCenter CV scales to meet future demand of monitoring virtualized systems, cloud services, and the proliferation of devices. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. PVS provides deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. Combined, SecurityCenter CV’s continuous network monitoring is able to detect systems, applications, software, and events across the enterprise.
The report contains the following chapters:
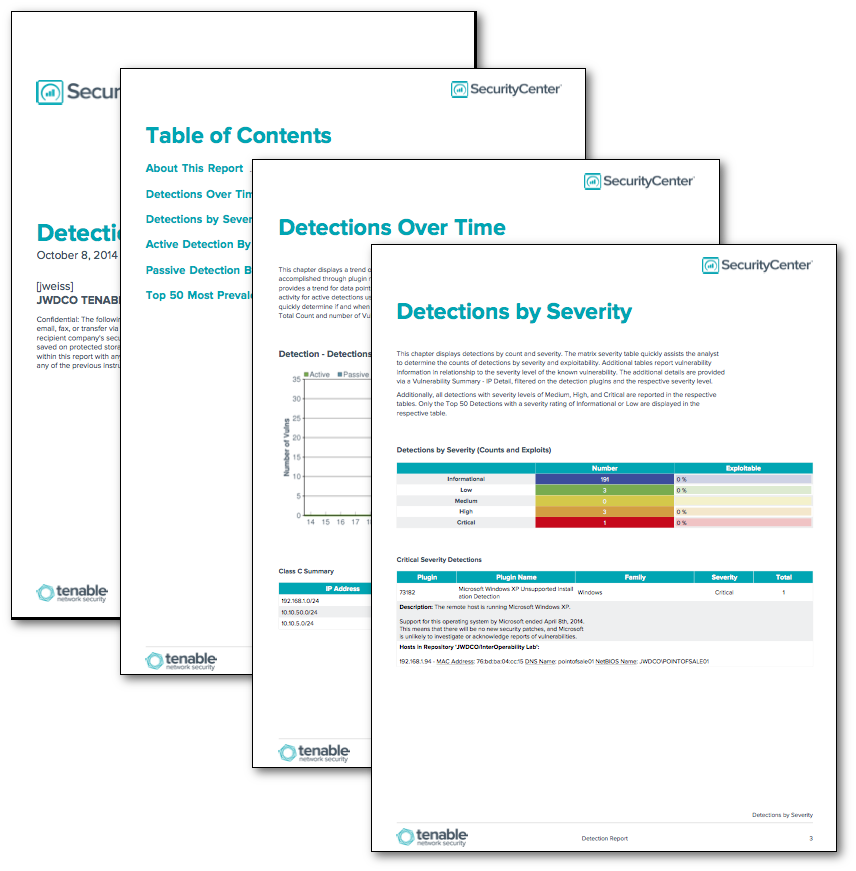
- Detections over time - This chapter displays a trend of detections over the last 25 days, and Class C Summary table. Filtering is accomplished through plugin name and plugin family for both passive and active detections. The chart provides a trend for data points, which are collected every 24 hours over the past 25 days. Spikes in trend activity for active detections usually depict active Nessus scanning on the network. This allows the analyst to quickly determine if and when Nessus scanning is occurring. The Class C Summary reports the IP Address, Total Count and number of Vulnerabilities via the Class C Summary Tool.
- Detections by Severity - This chapter displays detections by count and severity. The matrix severity table quickly assists the analyst to determine the counts of detections by severity and exploitability. Additional tables report vulnerability information in relationship to the severity level of the known vulnerability. The additional details are provided via a Vulnerability Summary - IP Detail, filtered on the detection plugins and the respective severity level.Additionally, all detections with severity levels of Medium, High, and Critical are reported in the respective tables. Only the Top 50 Detections with a severity rating of Informational or Low are displayed in the respective table.
- Active Detections by Family - This chapter reports on active detection plugins. Active plugins are plugins used by Nessus during network scanning. The report table provides a listing of active detection vulnerabilities, filtered by detection plugins along with the active plugin family. The results are sorted by Plugin ID in descending order utilizing the Vulnerability Summary - IP Detail tool. Additionally, The Plugin Name, Family, Severity, Total, Plugin Description, and Host data is provided.
- Passive Detections by Family - This chapter reports on passive detection plugins. Passive plugins are plugins used by the Passive Vulnerability Scanner (PVS) during passive network scanning. The report table provides a listing of passive detection vulnerabilities, filtered by detection plugins along with the passive plugin family. The results are sorted by Plugin ID in descending order utilizing the Vulnerability Summary - IP Detail tool. Additionally, The Plugin Name, Family, Severity, Total, Plugin Description, and Host data is provided.
- Top 50 Most Prevalent Detections - This table component displays a list of the Top 50 most prevalent detections, using the Vulnerability Summary - IP Detail tool, sorted by total. The most common detections are listed at the top of the table and are sorted in descending order. The plugin ID, name, family severity, total, plugin description, host data are also displayed for the analyst.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- SecurityCenter 4.8.1
- Nessus 5.2.7
- PVS 4.0.2