사이버 보안 스냅샷: 바로 지금 중요한 6가지 사항

Topics that are top of mind for the week ending July 15 | Government cybersecurity efforts tripped by technical debt. Neglect SaaS security at your own risk. A ranking of the most dangerous software weaknesses. Lessons learned about critical infrastructure security. And much more!
1 – Don’t downplay SaaS security
IT, security and compliance teams pay close attention to Infrastructure- and Platform-as-a-Service (IaaS and PaaS) offerings, but they often overlook the tens or even hundreds of Software-as-a-Service (SaaS) applications used across their organizations, increasing their risk of data breaches.
That’s the main message from the Cloud Security Alliance’s “SaaS Governance Best Practices for Cloud Customers,” a report that outlines risks involved in SaaS adoption and usage, and details how to protect data within SaaS environments.
“While SaaS providers handle much of the responsibility in the Shared Responsibility Model, SaaS consumers are still largely responsible for data governance and access control. This means ensuring who has access to what data, what level of permissions, and under what context,” the report reads.
For example, organizations must make key decisions around:
- Encryption key management
- 취약성 관리
- Backup and storage
- Incident response and business continuity plans
- Regulatory compliance
- Third-party vendor risk
Want to learn more about security best practices for SaaS deployments?
- “Key takeaways from CSA’s SaaS Governance Best Practices guide” (CSO Magazine)
- “SaaS and Third-Party Risk: Is Your Organization Asking the Hard Questions?” (DarkReading)
- “Why your SaaS configurations are putting you at risk” (TechBeacon)
- “SaaS Outages: When Lightning Strikes, Thunder Rolls” (Forrester)
- “Cloud Security: 3 Things InfoSec Leaders Need to Know About the Shared Responsibility Model” (Tenable)
2 – MITRE: Beware these dangerous software weaknesses
Here’s a new report that can help you mitigate your security risks: the “2022 CWE Top 25 Most Dangerous Software Weaknesses.” In this annual ranking, MITRE lists the most common and impactful software weaknesses, all of which attackers can easily find and exploit to take over a system, steal data or torpedo applications. Weaknesses encompass flaws, faults, bugs or other errors in implementation, code, design or architecture.
Topping this year’s list is “Out-of-bounds Write,” in which software writes data either past the end or before the beginning of the intended buffer, which can result in data corruption, a crash or code execution. Suggested mitigations include:
- Choosing a language and a vetted library that don’t allow this weakness to occur or that provide a construct that makes this weakness easier to avoid.
- Run or compile the software using features or extensions that automatically provide a protection mechanism that mitigates or eliminates buffer overflows.
- Run or compile the software using features or extensions that randomly arrange the positions of a program's executable and libraries in memory.
Each entry on the list is linked to a dedicated page for it brimming with details, context, mitigation recommendations and examples.
Rounding out the top five are:
This list is compiled by the team behind the CWE (Common Weakness Enumeration) community-developed list of software and hardware weaknesses. CWE is sponsored by the Cybersecurity and Infrastructure Security Agency (CISA) and managed by the Homeland Security Systems Engineering and Development Institute (HSSEDI), which is operated by MITRE.
To choose and rank the weaknesses, the CWE team leveraged Common Vulnerabilities and Exposures (CVE) data from the National Institute of Standards and Technology (NIST) National Vulnerability Database and the Common Vulnerability Scoring System (CVSS) scores associated with each CVE record, including CVE records from the CISA Known Exploited Vulnerabilities catalog.
More information:
- “CWE Top 25: These are the most dangerous software weaknesses of 2022” (The Daily Swig)
- “NVD CWE Slice” (NIST)
- “Mitre CWE - Common Weakness Enumeration” (SANS Internet Storm Center)
3 – IDC: U.S.government cybersecurity teams grapple with technical debt
Barriers to the success of cybersecurity initiatives vary among federal, state and local governments, but there’s a common challenge to all: high levels of technical debt.
That’s according to IDC’s “Government Buyer Intelligence Survey: Analysis of Trends in Cybersecurity Across Federal, State and Local Agencies” presentation, based on a poll of 1,315 IT and non-IT government decision makers.
Technical debt hampers government cybersecurity priority efforts, such as ransomware risk reduction, citizen privacy protection, faster incident response and increased trust in public services, the presentation states. Here’s an IDC chart with more details:
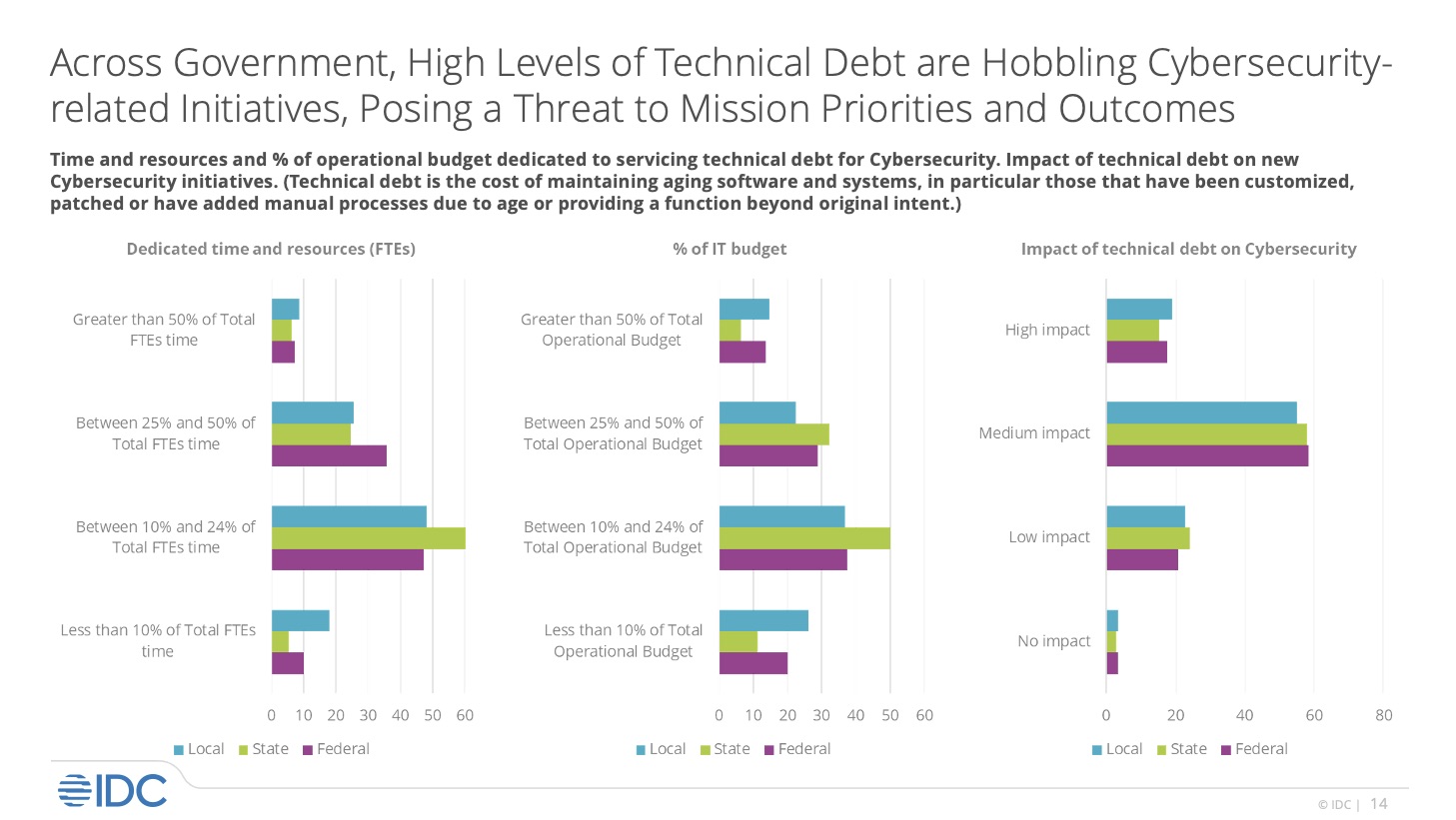
On the flip side, the cybersecurity investment priorities of local, state and federal governments include cloud security, network security, vulnerability management/assessment, threat hunting and next-gen firewalls.
(Source: IDC “Analysis of Trends in Cybersecurity Across Federal, State, and Local Agencies”, Doc # US49144722, May 2022.)
To get more information about technical debt in government, read:
- “Tech Debt is the Biggest Cyber Vulnerability, NSA’s Joyce Says” (MeriTalk)
- “How Federal Agencies Can Identify and Address Technical Debt” (FedTech)
- “What Is Technical Debt in State and Local Governments?” (StateTech)
4 – What have we learned about securing critical infrastructure?
With cyberattacks against critical infrastructure rising, what insights and lessons can we draw from well-known vulnerabilities and recent attacks against these essential assets and resources of society?
That’s the question Tenable Senior Research Manager Giuliana Carullo tackles in her blog “Securing Critical Infrastructure: What We've Learned from Recent Incidents.” Carullo surveys the evolution of critical infrastructure security, pinpoints the challenges of managing vulnerabilities in these environments, and zeroes in on the Colonial Pipeline ransomware attack.
She also highlights the following vulnerabilities, which have affected this sector in different ways:
| CVE | 설명 | CVE Rating |
|---|---|---|
| CVE-2014-0160 | Heartbleed | High |
| CVE-2020-11896, CVE-2020-11897, CVE-2020-11901 (out of 19) | Ripple20 | Medium to Critical |
| CVE-2021-35211 | Remote code execution (RCE) vulnerability in the SolarWinds Serv-U | Critical |
| CVE-2021-20016 | SonicWall SSLVPN Vulnerability - attack initiation | Critical |
| CVE-2020-1472 | Netlogon Elevation Privilege Escalation- privilege escalation | Critical |
Want to learn more about critical infrastructure security? Check out these Tenable resources:
- “How Can We Strengthen the Cybersecurity of Critical Infrastructure?” (blog)
- “The State of OT Security, a Year Since Colonial Pipeline” (blog)
- “The State of OT Security, a Year Since Colonial Pipeline” (podcast)
- “Colonial Pipeline One Year Later: What Have (and Haven’t) We Learned?” (LinkedIn Live)
5 – The U.S. government takes on cloud security
Cloud security is top of mind for all organizations using SaaS, IaaS and PaaS offerings, and the U.S. government is no exception. Curious to learn Uncle Sam’s most recent thoughts on this topic? Check out version 2.0 of CISA’s Cloud Security Technical Reference Architecture.
The document, whose first version came out in August 2021, recommends approaches to cloud migration and data protection so that federal agencies and departments can detect, respond and recover from cyber incidents. It also seeks to help the federal government improve cybersecurity across the board, while understanding the benefits and risks of adopting cloud services. The 70-page paper focuses on three key areas: shared cloud services, cloud software design and cloud security posture management.
For more information read:
- “CISA releases second version of secure cloud migration guidance for agencies” (FedScoop)
- “CISA Posts Updated Cloud Security Technical Reference Architecture” (ExecutiveGov)
- “CISA's Cloud Security Technical Reference Architecture: Where it succeeds and where it falls short” (CSO Magazine)
6 – Our takeaways from Forrester AppSec tips for security leaders
And finally, there’s this: Applications remain the main vector for external breaches, according to Forrester’s “The State of Application Security, 2022” report. Factors driving this trend include a growth in:
- Open source vulnerabilities
- Attacks against the software supply chain
- Malicious API traffic
- Use of improperly secured containers
Forrester recommendations for security leaders include:
- As they juggle multiple priorities, they should delegate tactical decisions about application security to development teams, which increasingly pick their security tools and control the budget for these products.
- With the added time, security leaders should focus on securing their organizations’ product lifecycle to help the business “secure what they sell, increase time-to-market, deliver customer value, and deploy continuously with confidence.”
- Move from “shift left” to “shift everywhere” by expanding security scanning throughout the software development lifecycle. With this approach, product teams can “develop and deploy with speed and confidence.”
For more information:
- Read the full report (available to Forrester subscribers and for purchase)
- Read the Forrester blog post "The Secure Everywhere Movement Is Here: Are You On Board?"
- Watch the Digital Anarchist interview with two of the report's authors
자세히 알아보기
- Cybersecurity Snapshot




Tenable One
데모 요청
전 세계에서 선도적인 AI 기반 위험 노출 관리 플랫폼입니다.
감사합니다
Tenable One에 관심을 가져 주셔서 감사합니다.
담당자가 곧 연락할 것입니다.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success