When Remote Work Isn't an Option: Industrial Security in the COVID-19 Era

For utilities and manufacturers tasked with keeping their lights on during the COVID-19 response, scaled-down workforces can pose increased security risks. Here's how to protect your teams and operations from internal and external threats.
No matter where in the world you are, the last several weeks have likely drastically altered the norms of daily life. With the COVID-19 pandemic rapidly circumnavigating the globe, nearly every business is changing the way they operate to adapt to a new normal. Wherever possible, many employees have been directed to work from home and utilize laptops, tablets, smartphones and conference bridge services.
But working from home is not always an option. For industries designated as “critical infrastructure” by local and national governments, a certain level of on-site work is required to keep basic needs like food, water, and energy flowing to their respective communities. These operations – which include food and beverage production, electrical and grid operations, oil and gas, shipping and transportation and water producers, among others – cannot scale down, pause operations, or easily transfer to a work-from-home model.
As this unprecedented public health crisis unfolds, manufacturers and critical infrastructure operators face the unique challenge of maintaining uptime and efficient production, within a fully secured environment. While most industrial operations are largely automated today, these connected systems can also be the Achilles’ heel of the entire operation.
Don’t overlook your OT security blind spots
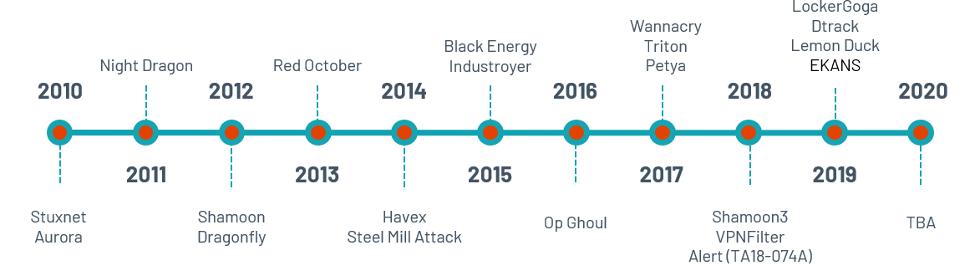
Operational technology (OT) environments face security risks that left unchecked could take down production or significantly alter a product enough to make it dangerous, even deadly. In some cases, the attack surfaces and number of attack vectors in OT environments have grown exponentially. In fact, at an industry-wide level, the amount and severity of attacks targeting OT networks continue to increase each year. And with the convergence of IT and OT, organizations are now experiencing the phenomenon of attacks that laterally creep between IT and OT. Clearly, there is a need to secure OT networks as we have in IT.
Assess the risks of your scaled-down workforce
On an ordinary day, critical infrastructure organizations maintain a security posture that satisfies their board, regulatory bodies and customers. But, what happens when unforeseen events, such as a global pandemic, disrupt routine operations? With a scaled-down workforce and non-essential employees confined to their homes, there is a greater potential for your security posture to slip simply because fewer people are available to maintain normal operations. This can lead to:
- Erroneous changes: Fewer people at the plant or on the production floor increases the possibility of someone misconfiguring a programmable logic controller (PLC), especially if a junior engineer less familiar with the process makes an inadvertent change.
- Delayed response: Due to short staffing, or the need to divert employees to other tasks, security personnel may be negatively impacted in their ability to react to alarms in a timely fashion.
- Opportunistic attacks: Nefarious activity will likely increase during this period as hackers look to exploit the procedural disruptions and overstretched skeleton crews associated with non-standard business operations.
Taking an honest look at these vulnerabilities is the first step to understanding which security measures need to be in place to keep critical operations running smoothly and safely.
Begin to play offense in your industrial security efforts
Even as the COVID-19 pandemic rapidly changes the playing field, industrial security doesn’t have to suffer. There are steps that utilities and manufacturers can take to protect their operational networks and empower staff to safely continue their work both on-site and from home. Continuity of service depends on a robust and resilient approach to OT security that includes:
- Ensuring full visibility of your IT/OT infrastructure. This includes both the global scope of your distributed network as well as drill-down capabilities into granular device information (e.g. serial number, OS, firmware). Secured-anywhere access to these unified dashboards can empower authorized personnel and remote staff to continue their routine monitoring and security as if they were in their normal office setting.
- Updating your mobile policy and alarm triggers. Notification chains for violations or questionable behaviors should reflect your newly remote and mobilized workforce. This means making sure each alert is finely tuned to reach the right person at the right time via the most relevant medium (such as phone, PC, or text), depending on whether the recipient is working on-site or remotely.
- Maintaining a paper trail of changes to industrial controllers. Configuration control should capture automated “snapshots” any time a PLC programming change occurs, preserving knowledge of the “last known good state” as well as who was on the network, what actions they took, and the subsequent results or interruptions. While malware may alter programming on a PLC, hazardous changes can just as easily come from a careless employee or junior engineer who is overworked, outside their usual role, or distracted due to other priorities.
For many critical industries, the sobering reality of the COVID-19 era is that business must continue, no matter how trying the circumstances.
Our ability to navigate this unscripted departure from normalcy requires deep situational awareness of both the macro and micro levels of operations. Survival will require grit and perseverance, and agile teams and systems that can grow and adapt alongside the organization. In the immortal words of Apollo 13 flight director Gene Kranz, the present situation demands nothing less than “our finest hour.”
By combining the right tools and attitude with the collective will of the security community, we can come through this tribulation stronger and more resilient than ever before.
More information on industrial cybersecurity
For additional ways to upgrade your OT security posture, here are some resources that can help:
- Watch the on-demand webinar, “5 Things You Need to Know About IT/OT Convergence”
- Check out the infographic on “The 7 Most Unsafe Gaps for Industrial Cybersecurity”
- Review the Industrial Cybersecurity checklist for key criteria to protect critical infrastructure
자세히 알아보기
- SCADA
- Vulnerability Management




Tenable One
데모 요청
전 세계에서 선도적인 AI 기반 위험 노출 관리 플랫폼입니다.
감사합니다
Tenable One에 관심을 가져 주셔서 감사합니다.
담당자가 곧 연락할 것입니다.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success