Ransomware has evolved into an ecosystem with multiple players and an expanded threat model. Ransomware groups now deploy a double extortion technique, where they both encrypt and exfiltrate their victims' data. The Tenable Security Research Team has released a report that enumerates common vulnerabilities exploited by ransomware affiliates and groups. The Ransomware Ecosystem dashboard enables organizations to quickly scan for the vulnerabilities commonly exploited by ransomware groups..
Organizations with effective Business Continuity and Disaster Recovery plans are protected against threats to availability of data, which can come in many forms, such as natural disasters, hardware failures, or malicious attacks. These organizations could recover operations from a traditional ransomware attack without paying the ransom. However, the vulnerabilities that gave ransomware groups the opportunity to successfully penetrate the infrastructure may still leave organizations open to significant risk. Like any good business, ransomware players discovered the advantage of threatening data confidentiality by publishing samples of their targets' sensitive data and threatening to expose all the data unless they are paid.
Threat actors understand the economic advantage of investing in the ransomware ecosystem, becoming more sophisticated and efficient over time. Organizations often struggle to secure a budget for resources needed to protect their infrastructure and prevent attacks from succeeding.
The Ransomware Ecosystem dashboard displays assets by plugin family along with associated vulnerabilities. Operations teams use this information to evaluate risk based on the organization's business priorities. The ability to rapidly mitigate vulnerabilities requires data to be presented in a concise manner focused on findings that pose the greatest risk to the organization. Risk managers leverage risk-based vulnerability management platforms to prioritize mitigation efforts.
Tenable.io enables organizations to quickly identify and locate vulnerabilities in their infrastructure. This dashboard displays the most common vulnerabilities sorted by platform type that are commonly exploited by ransomware groups. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. The requirement for this dashboard is: Tenable.io Vulnerability Management (Nessus).
Widgets
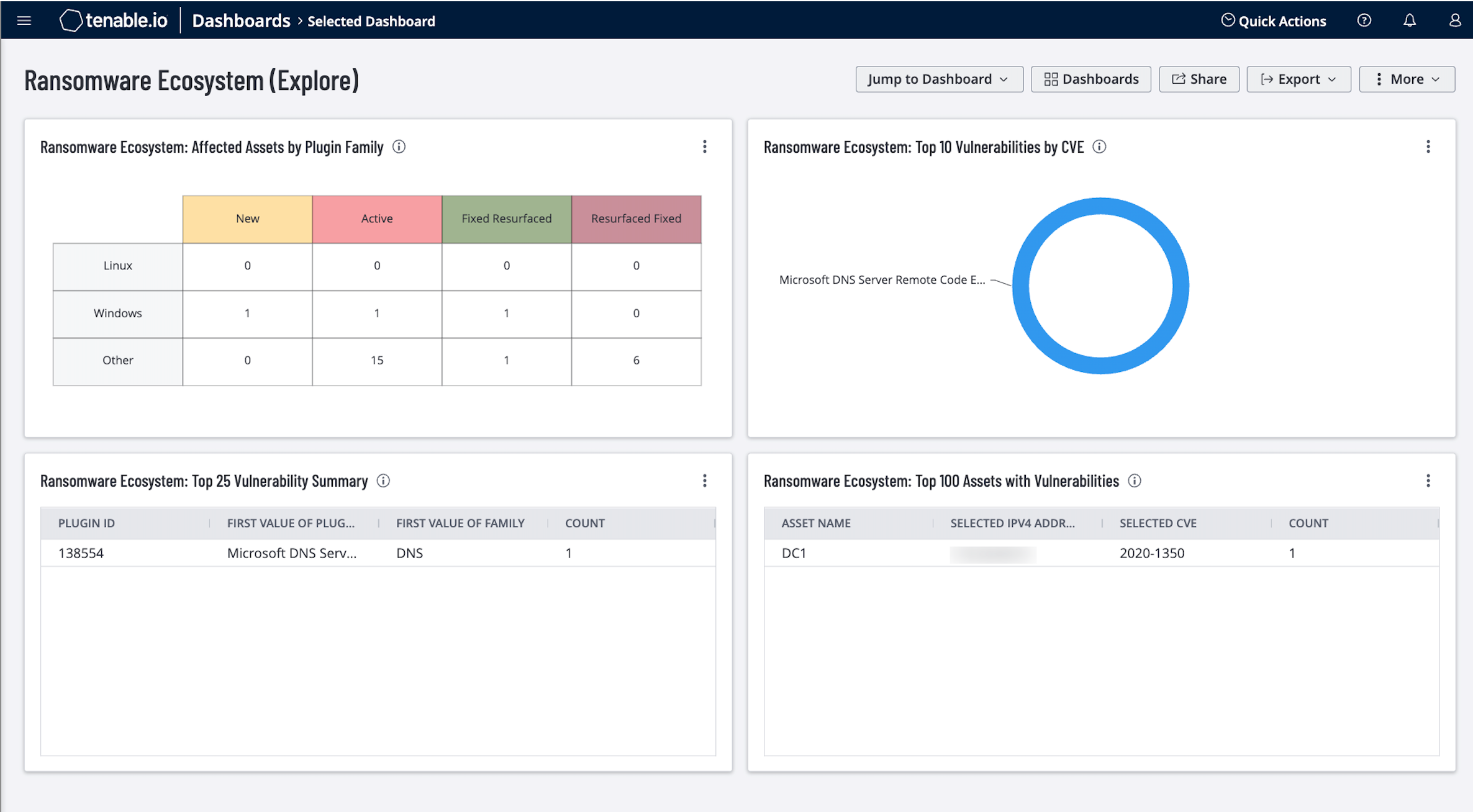
Ransomware Ecosystem: Affected Assets by Plugin Family – This widget uses the CVE, Plugin Family, and Vulnerability State filters to display counts of the vulnerabilities that have been identified as those used in ransomware attacks. The number of vulnerabilities that are identified as New, Active, Resurfaced, and Fixed are displayed for Windows, Linux, and other Operating Systems. A total of 77 CVEs are associated with this alert. Vulnerabilities identified and fixed are displayed using the referenced CVEs. Rows for Linux, Windows, and Other Operating Systems enumerate counts for the number of risks identified and fixed. This data helps organizations protect against threats to confidentiality and availability of data, as identified within the ransomware ecosystem. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).
Ransomware Ecosystem: Top 10 Vulnerabilities by CVE – This widget lists the top 10 vulnerabilities that put the organization at risk for ransomware attacks. Addressing these vulnerabilities first greatly reduces cyber risk. Information is filtered by CVE to display the vulnerabilities that are typically leveraged in ransomware attacks. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).
Ransomware Ecosystem: Top 25 Vulnerability Summary – This widget lists the top 25 vulnerabilities that put the organization at risk for ransomware attacks. Information is filtered by CVE to display the vulnerabilities that are vulnerable to ransomware. Results are sorted by total vulnerabilities. PluginID, PluginName, and Family are displayed in the table. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).
Ransomware Ecosystem: Top 100 Assets with Vulnerabilities – This widget lists the top 100 assets at risk for vulnerabilities leveraged in ransomware attacks. Addressing these assets first greatly reduces cyber risk. Information is filtered by CVE to display counts of the vulnerabilities for assets that are vulnerable to ransomware attacks. Results are sorted by total vulnerabilities. Asset name, IPv4 Address, and identified CVE(s) are displayed in the table. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success