Manage and Remediate Cloud Infrastructure Misconfiguration Vulnerabilities with Tenable.cs and HashiCorp Terraform Cloud

Cloud breaches are on the upswing due to preventable misconfigurations. Here’s how you can lower your risk with a new integration between Tenable.cs and Terraform Cloud.
Today’s cloud environments are highly dynamic with new updates continuously released into production and workloads scaling up and down based on customer demand. Within minutes cloud engineers can spin up and fully deploy resources to the cloud. But with increased speed many times comes increased risk. System vulnerabilities caused by misconfigurations are often overlooked and may remain undetected for months. As a result, cloud breaches are increasing in scale and velocity. Over 30 billion records were exposed in 200 breaches between 2018 and 2020 due to cloud infrastructure misconfigurations alone.
How can you reduce your chances of suffering breaches caused by cloud misconfigurations? In this post, we explain how Tenable and HashiCorp can help with this issue via a new integration between Tenable.cs and Terraform Cloud Run Tasks.
Introduction to cloud provisioning and Terraform
Cloud resource provisioning is a key aspect of deploying cloud workloads. Although most cloud providers have their own provisioning utilities, best-of-breed tools like Hashicorp Terraform offer benefits that go beyond what cloud providers offer. Using Terraform, an open-source Infrastructure as Code (IaC) tool, to provision infrastructure provides many benefits to the management and operations of your environment. HashiCorp Configuration Language (HCL) provides the ability to standardize reusable modules of infrastructure that can be used across projects and environments. When standing up infrastructure, Terraform reads the current state of your environment and determines any changes needed to configure the environment to the state defined in your IaC. This simplifies the process of managing complex architectures which can be fragile if manually maintained. IaC allows for the code to be version controlled and provides better visibility into how the infrastructure has been provisioned and configured.
Terraform key security considerations
Terraform also offers security benefits. The workflow around infrastructure provisioning can be used to protect your environment from security issues. When enforcing the use of IaC for any changes in your environment, code can be assessed to ensure that any security defects are detected and mitigated before infrastructure is provisioned. Security or operational guardrails can be codified and enforced through CI/CD pipelines, gates, or other automated means to ensure that your environment is compliant with your policies.
While using tools such as Terraform simplify managing infrastructure, it’s still common for critical misconfigurations of cloud infrastructure to happen. Key areas of concerns for vulnerability management for Terraform environments include:
- Secrets Management: Terraform requires credentials in order to authorize any API actions necessary to provision the infrastructure specified in your code. Since these credentials provide privileged access to create, manage, and destroy your environment, care should be taken to ensure that they are not exposed to unauthorized people or processes.
- System State Management: Terraform uses a state file to track the state of provisioned infrastructure resources. By default, the state file is stored on the local file system of the system where Terraform is executed. Persisting state files with your source code is a bad idea as these could contain secrets or other sensitive information.
- Dependency Management: Terraform uses plugins called “providers” to interact with remote APIs for the resources defined in your code. These are downloaded to the system where Terraform is executed when performing the “terraform init” command. As providers manage powerful operations in your infrastructure, it is important to download these from trusted sources and confirm that they have not been tampered with prior to using them.
- Drift Management: In any complex enterprise environment, manual changes can occur in runtime through “break the glass” mechanisms or other means. These changes cause a deviation, referred to as “drift,” between your runtime environment and what has been defined in your Terraform code. If not corrected in the source code, build teams will continue to use the old version and/or systems will no longer meet security requirements.
For more on Terraform security key considerations read the whitepaper “DevOps Guide to Terraform Security”.
Preventing Terraform vulnerabilities with Tenable.cs
Tenable.cs is a developer-friendly, Cloud-Native Application Security Platform (CNASP) that enables your organization to secure cloud resources, container images and cloud assets, providing end-to-end security from code to cloud to workload. To enforce best practices, you can evaluate your code using a static code analysis tool such as Terrascan. Terrascan is an open source project that was created by Tenable and is the underpinning scanning engine for Tenable.cs. Terrascan includes hundreds of policies across multiple providers written in the Rego language, and assesses for misconfigurations using the Open Policy Agent (OPA) engine. These policies can be extended to include any standards specific to your environment. To enforce these as part of your workflow, you can include a job as part of your CI/CD pipeline that uses Terrascan to scan any changes to your HCL files for security issues. If any issues are detected, the job will fail with an error message indicating that a security issue has been found that needs to be addressed.
Tenable.cs enables cloud operations and security teams to assess Terraform templates for policy violations. You can integrate cloud infrastructure security into the DevOps pipeline to prevent security issues from reaching production. You can also quickly remediate IaC misconfigurations directly in development tools to enforce policies in both build-time and runtime.
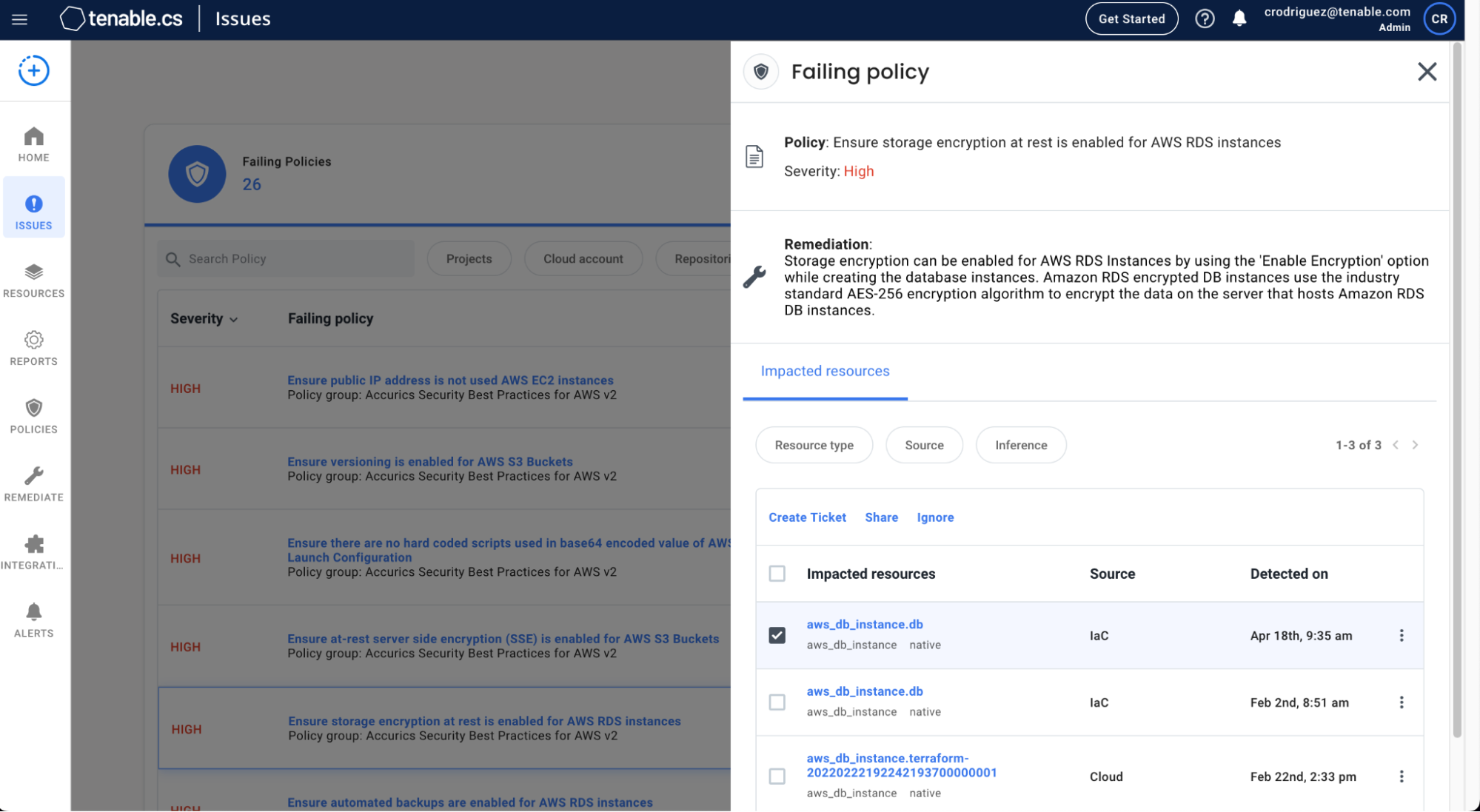
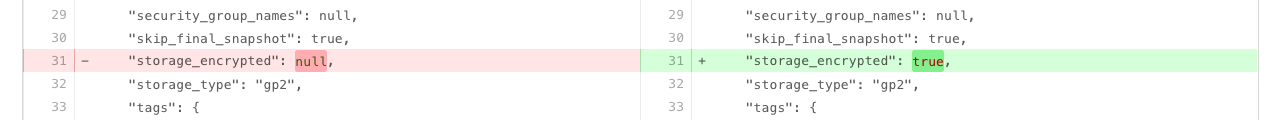
New! Enhanced automated remediation support with HashiCorp Terraform Cloud Run Tasks
Now Tenable is boosting its capabilities for securing Terraform with support for HashiCorp's new Terraform Cloud Run Tasks. Terraform Cloud provides a hosted solution to build and deploy Terraform Templates. Using the new Terraform Cloud Run Tasks, you can leverage Tenable.cs to scan your Terraform Templates during the Terraform cloud deploy step. The integration allows Terraform Cloud customers to detect any security issues within their IaC using Tenable.cs as part of the planning phase of the Terraform execution. By adding this support for Terraform Cloud Run Tasks in Tenable.cs, we’re helping developers detect and fix compliance and security risks in their IaC so they can mitigate issues before cloud infrastructure is provisioned.
Additionally, knowing the exact remediation steps can be time intensive and challenging. That’s why remediation recommendations are provided as part of the integration, in the form of a pull request to the source code repository associated with the Terraform workspace, to help with fixing issues found in Terraform templates before they are provisioned. Customers can leverage over 1,500 policies in the Tenable.cs commercial offering to perform deep scans in Terraform Cloud. Users interested in viewing the setup guide on how to connect Tenable.cs with Terraform Cloud Workspace can find detailed documentation here.
To learn more about Tenable.cs view the data sheet or access the on-demand webinar “Introducing Tenable.cs: Secure Every Step From Code to Cloud”.
Learn more
- Announcements
- Cloud




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success