Microsoft’s February 2023 Patch Tuesday Addresses 75 CVEs (CVE-2023-23376)
Microsoft addresses 75 CVEs including three zero-day vulnerabilities that were exploited in the wild.
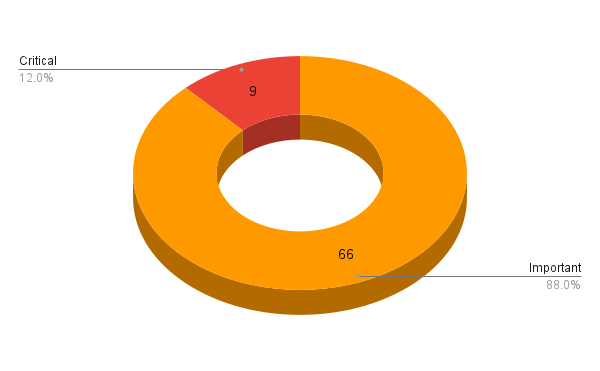
- 9Critical
- 66Important
- 0Moderate
- 0Low
Microsoft patched 75 CVEs in its February 2023 Patch Tuesday Release, with nine rated as critical and 66 rated as important.
This month’s update includes patches for:
- .NET and Visual Studio
- .NET Framework
- 3D Builder
- Azure App Service
- Azure Data Box Gateway
- Azure DevOps
- Azure Machine Learning
- HoloLens
- Internet Storage Name Service
- Microsoft Defender for Endpoint
- Microsoft Defender for IoT
- Microsoft Dynamics
- Microsoft Edge (Chromium-based)
- Microsoft Exchange Server
- Microsoft Graphics Component
- Microsoft Office
- Microsoft Office OneNote
- Microsoft Office Publisher
- Microsoft Office SharePoint
- Microsoft Office Word
- Microsoft PostScript Printer Driver
- Microsoft WDAC OLE DB provider for SQL
- Microsoft Windows Codecs Library
- Power BI
- SQL Server
- Visual Studio
- Windows Active Directory
- Windows ALPC
- Windows Common Log File System Driver
- Windows Cryptographic Services
- Windows Distributed File System (DFS)
- Windows Fax and Scan Service
- Windows HTTP.sys
- Windows Installer
- Windows iSCSI
- Windows Kerberos
- Windows MSHTML Platform
- Windows ODBC Driver
- Windows Protected EAP (PEAP)
- Windows SChannel
- Windows Win32K
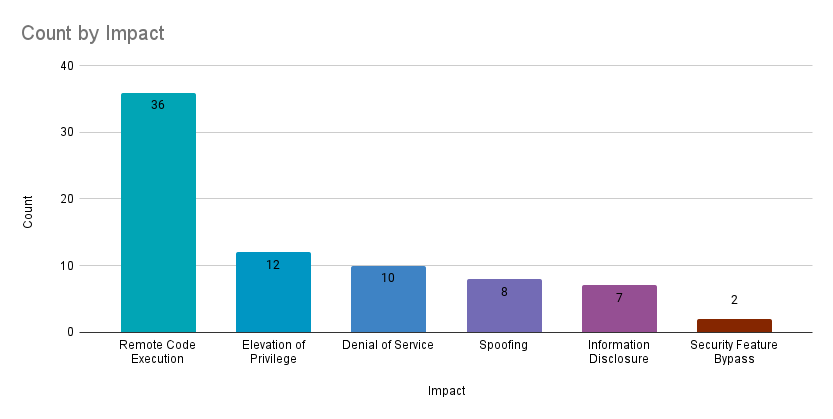
Remote code execution (RCE) vulnerabilities accounted for 48% of the vulnerabilities patched this month, followed by elevation of privilege (EoP) vulnerabilities at 16%.
CVE-2023-23376 | Windows Common Log File System Driver Elevation of Privilege Vulnerability
CVE-2023-23376 is an EoP vulnerability in Windows operating systems receiving a CVSSv3 score of 7.8 that has been exploited in the wild. The vulnerability exists in the Common Log File System (CLFS) Driver, a logging service used by kernel-mode and user-mode applications. This vulnerability can be exploited after an attacker has gained access to a vulnerable target in order to elevate to SYSTEM privileges.
In 2022, Microsoft patched two EoP vulnerabilities in CLFS, CVE-2022-37969 and CVE-2022-24521, that were also exploited in the wild. CVE-2022-24521 was disclosed to Microsoft by the National Security Agency and CrowdStrike, and patched in Microsoft April Patch Tuesday. CVE-2022-37969 was patched in Microsoft's September Patch Tuesday.
CVE-2023-21529, CVE-2023-21706, CVE-2023-21707 and CVE-2023-21710 | Microsoft Exchange Server Remote Code Execution Vulnerability
CVE-2023-21529, CVE-2023-21706, CVE-2023-21707 and CVE-2023-21710 are RCE vulnerabilities in supported versions of Microsoft Exchange Server. CVE-2023-21710 received a CVSSv3 score of 7.2 while the other three CVEs were assigned CVSSv3 scores of 8.8. The vulnerabilities allow a remote attacker to execute arbitrary code on a vulnerable server, via a network call. CVE-2023-21529, CVE-2023-21706, CVE-2023-21707 were given a rating of "Exploitation More Likely" on Microsoft's Exploitability Index.
CVE-2023-21529, CVE-2023-21706 and CVE-2023-21707 share similarities with CVE-2022-41082, an authenticated RCE publicly disclosed in September 2022 that was a part of the ProxyNotShell attack chain, a variant of the ProxyShell attack chain discovered in August 2021. Microsoft released mitigations in September to protect vulnerable servers until a patch was released in their November 2022 Patch Tuesday. A bypass of this mitigation, called OWASSRF (CVE-2022-41080), was then released in December 2022. Our recent blog on ProxyNotShell, OWASSRF and TabShell discusses these vulnerabilities in greater detail.
CVE-2023-21689, CVE-2023-21690 and CVE-2023-21692 | Microsoft Protected Extensible Authentication Protocol Remote Code Execution Vulnerability
CVE-2023-21689, CVE-2023-21690 and CVE-2023-21692 are RCE vulnerabilities in Windows operating systems and have been given a CVSSv3 score of 9.8. The flaw lies in the Protected Extensible Authentication Protocol (PEAP) server component, which is used to establish secure connections with wireless clients. Successful exploitation allows a remote, unauthenticated attacker to execute arbitrary code. For a target to be vulnerable, it must be running Network Policy Server and configured with a network policy that allows PEAP. All three vulnerabilities were rated as "Exploitation More Likely" according to their advisories.
An additional RCE affecting PEAP, CVE-2023-21695, has also been patched this month. However, exploitation for this flaw does require authentication. All four of these CVEs could be exploited using a crafted PEAP packet sent to an unpatched host.
CVE-2023-21823 | Windows Graphics Component Elevation of Privilege Vulnerability
CVE-2023-21823 is an EoP vulnerability in the Microsoft Windows Graphics Component. It received a CVSSv3 score of 7.8 and was exploited in the wild as a zero day. Exploitation of this flaw requires an attacker to log onto a vulnerable system and execute a specially crafted application. Successful exploitation would grant an attacker the ability to to run processes in an elevated context. While details have not been shared, the flaw is credited to researchers Genwei Jiang and Dhanesh Kizhakkinan of Mandiant.
CVE-2023-21715 | Microsoft Office Security Feature Bypass Vulnerability
CVE-2023-21715 is a security feature bypass vulnerability in Microsoft Office that was given a CVSSv3 score of 7.3 and was exploited in the wild. To be exploited, the vulnerability requires a local, authenticated user to download and open an attacker-created file on a vulnerable system. An attacker would need to entice the user to download and execute the file in order to successfully exploit this flaw. This flaw is credited to Hidetake Jo.
CVE-2023-21716 | Microsoft Word Remote Code Execution Vulnerability
CVE-2023-21716 is a RCE vulnerability in several versions of Microsoft Word, Sharepoint, 365 Apps and Office for Mac with a CVSSv3 score of 9.8. Although the vulnerable component is not specified, Microsoft states that the Preview Pane in these applications is an attack vector. The vulnerability can be exploited by an unauthenticated attacker sending an email with a rich text format (RTF) payload, which when opened, allows for command execution. The Microsoft advisory for this CVE links to MS08-026 and KB922849 for guidance on how to prevent Microsoft Office from opening RTF documents from unknown or untrusted sources by using the Microsoft Office File Block policy.
Tenable Solutions
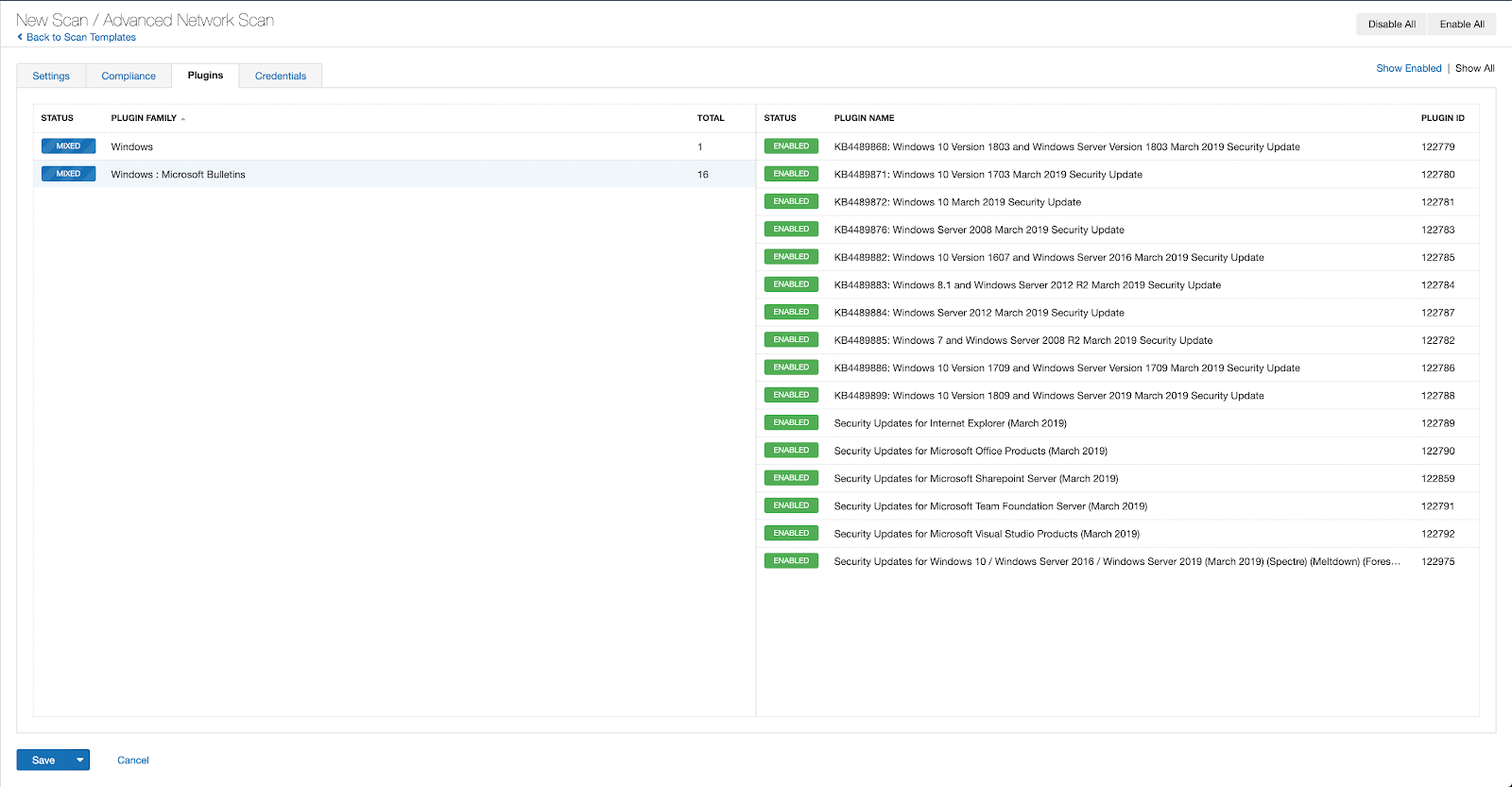
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name contains February 2023.
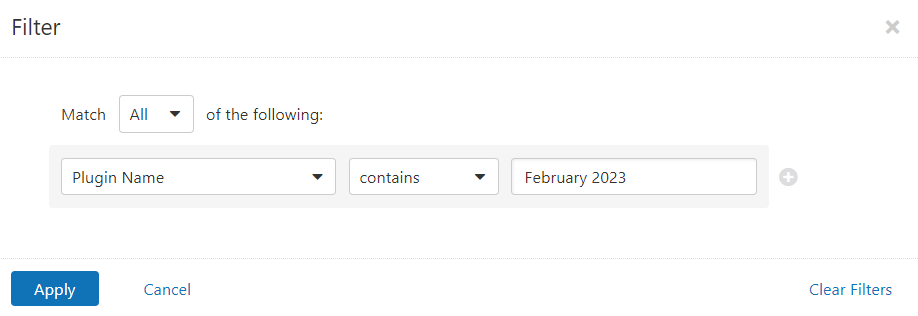
With that filter set, click the plugin families to the left and enable each plugin that appears on the right side. Note: If your families on the left say Enabled, then all the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
A list of all the plugins released for Tenable’s February 2023 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
Get more information
- Microsoft's February 2023 Security Updates
- Tenable plugins for Microsoft February 2023 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
Learn more
- Exposure Management
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success