by Cesar Navas
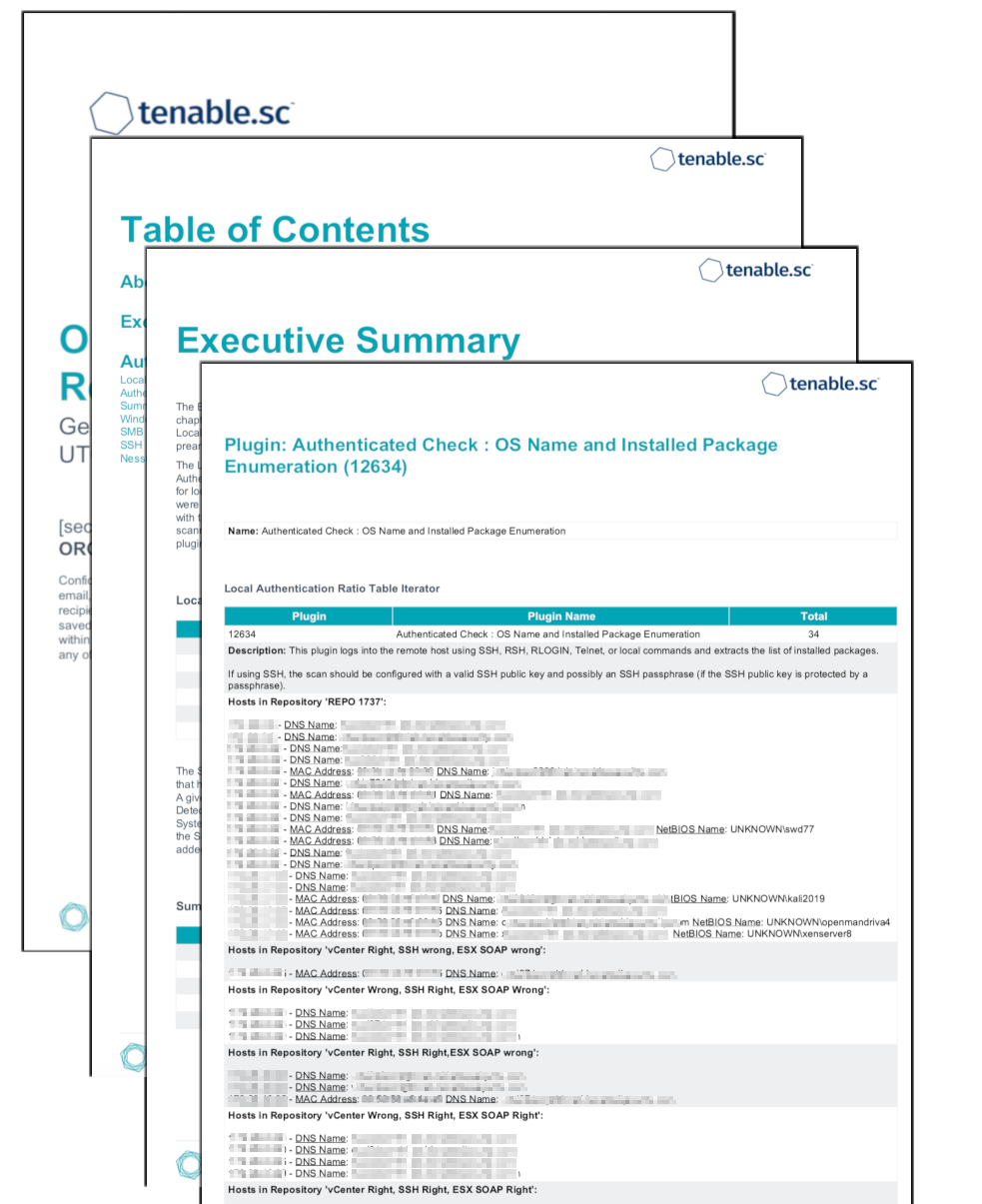
Cyber Exposure requires the data collected by the vulnerability scanner to be trusted and verifiable. Nessus provides several plugins that assist in understanding the scan status and provides a level of trust to risk managers. This report brings together all the plugins used to determine if an asset was successfully authenticated during the vulnerability scan. This report includes tables showing all the hosts that have had the respective plugins fire, along with iterators to define how the data is sorted. Lastly, this report will supply a system administrator with the details, like host address or plugin description, that may be needed to take appropriate action to correct any issue.
Authentication is connecting to a system and providing credentials in order to gain access to the system. Nessus scans systems by using different network protocols (SSH, SMB, HTTPS, SNMP, etc.) in order to gain access to the remote target asset. For example, logging in to a remote host via SSH using a username and password is a method of authentication. Each remote asset can authenticate using several protocols. Assets with more than one authentication protocol, for example Windows server running a SQL server, could report both authentication success and failure. Understanding this fact during analysis is key to understanding if or why the system was successfully scanned or not. While in many cases the successful authentication of an asset may seem binary, there are many examples of successful scanning systems with authentication failures. With this report, not only are the many examples of authentication successes/failures shown but also the host addresses and description of the issue is highlighted. The system administrator should review all the failures, by going through the tables after the host count matrices, and understand the services which are enabled on the asset for a complete. analysis.
Local checks are a feature in Nessus scans which enable the scanner to perform security checks on the target asset. Different authentication protocols may allow for general checks to be performed locally, but when all possible checks are completed, Nessus does a more detailed local check. The local check always requires authentication and often requires elevated privileges. By breaking down the plugins related to local checks, a system administrator is able to identify the exact hosts that are authenticating properly or are not. Local checks for major operating systems with security advisories numbering in the thousands are often grouped into their own plugin family, but local checks plugins also exist in other families such as Firewalls or Misc.
Enabling local checks is much more complex than authentication, and occurs after successful authentication has been established. In order to enable local checks, the following criteria must be satisfied:
-
The target device or operating system must be identified
-
Local checks must be available in Nessus plugins for the identified device or operating system
-
The information needed to enable local checks for that particular device or operating system must be obtained from the remote host
-
Except in particular circumstances, such as scanning localhost, remote authentication must first be successful before local checks can be enabled - but the threshold for enabling local checks is higher than the threshold for successful authentication.
Local checks are a requirement to ensure all scan reports are complete and accurate. Users can enable local checks by providing credentials with elevated privileges and/or administrative access, or by deploying Nessus Agent. Without elevated access, the ability for Nessus to successfully identify risk on a system is diminished. The more access to a system Nessus has, the more complete the risk analysis is.
This report provides the organization with a clear and simplified method to track and troubleshoot authentication related problems. By grouping authentication plugins into diagnostic context, the report allows administrators to apply focus to areas of concern. Furthermore, this report drills into each matrix and table to further illustrate the state of credentialed scans. The data helps to facilitate the Fix and Measuring steps to the Cyber Exposure Lifecycle. Tenable.sc is the on-prem solution for gaining a comprehensive picture of the network, while keeping the data under the organization’s control. Built on leading Nessus technology, Tenable.sc discovers unknown assets and vulnerabilities, and monitors unexpected network changes before they turn into breaches.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success