by John Thounhurst
April 8, 2026
Organizations face persistent challenges in managing software vulnerabilities, particularly those affecting Java runtime environments and development frameworks. The Risk Manager must contend with continuously evolving exposure landscapes where patches may lag behind vulnerability disclosure, leaving infrastructure temporarily defenseless. Tenable Vulnerability Management (VM) provides a structured approach to identifying, analyzing, and prioritizing software exposures through integrated visibility and risk-based metrics.
The data collected by Tenable VM establishes a foundation for Exposure Management (EM) by correlating vulnerability data with asset criticality and exploit likelihood. Risk Managers gain the ability to differentiate between theoretical vulnerabilities and those representing genuine threats to business operations. This report provides an executive-level perspective on the organization's exposure footprint, while simultaneously providing granular operational detail. Security Operations Teams leverage these findings to construct remediation workflows that align technical effort with strategic risk reduction objectives.
Unsupported software versions represent a category of exposure that requires distinct handling as vendor patches typically become unavailable once support lifecycles conclude. The Unsupported Java Version chapter identifies installations operating beyond manufacturer support boundaries, forcing Risk Managers to evaluate alternative security controls and migration timelines. The Java Exposure Counts by Severity chapter segments vulnerabilities by criticality ratings, enabling Security Operations Teams to calibrate response intensity based on potential impact. The combination of severity-based segmentation and support lifecycle awareness creates a comprehensive view of the exposure landscape.
Asset-centric analysis complements vulnerability-centric perspectives by revealing concentration patterns that indicate systemic risk. The Hosts with the Most Java Vulnerabilities chapter identifies systems carrying disproportionate exposure burdens, directing remediation resources toward infrastructure components with the greatest aggregate risk. The Hosts with the Most Java Installation Detections chapter distinguishes between vulnerable configurations and informational findings, preventing confusion between actual exposures and inventory data. Risk Managers utilize these asset-focused chapters to understand where vulnerabilities cluster and whether concentration patterns reflect architectural decisions or operational gaps.
Predictive risk scoring enhances traditional severity metrics by incorporating threat intelligence and exploit probability into prioritization decisions. The Top Java Exposures by Tenable Vulnerability Priority Rating (VPR) chapter applies machine learning models to identify vulnerabilities with elevated exploitation likelihood, shifting focus from theoretical maximum impact to probable real-world attack scenarios. The Java Installation Details chapter provides comprehensive configuration visibility, supporting both vulnerability validation and compliance verification activities. Security Operations Teams integrate VPR-based prioritization into patch management workflows to address the most dangerous exposures before moving to lower-probability threats.
The integration of Java vulnerability visibility, predictive analytics, and asset-centric perspectives enables organizations to see the complete attack surface, predict which exposures warrant immediate attention, and act with confidence based on business-contextualized risk data. Risk Managers transition from reactive vulnerability management to proactive exposure reduction by understanding not just what vulnerabilities exist, but where concentrations occur, which installations lack vendor support, and which exposures present the highest probability of exploitation. Security Operations Teams gain the operational intelligence needed to defend the organization efficiently, directing finite remediation resources toward the findings that genuinely threaten business value, reputation, and stakeholder trust.
Chapters
Executive Summary: This chapter establishes a comprehensive foundation for understanding the organization's vulnerability posture related to Java runtime environments and associated frameworks. Risk Managers require this executive-level perspective to assess the scope of exposure management efforts and communicate risk levels to stakeholders. The chapter applies filters that restrict visibility to actively detected findings, excluding accepted risks and already-remediated vulnerabilities.
Unsupported Versions of Java: Organizations operating software versions beyond manufacturer support lifecycles face unique challenges because traditional patch-based remediation becomes unavailable. This chapter identifies installations running versions for which vendors no longer publish security updates. Risk Managers utilize this chapter to forecast future exposure management challenges and plan migration initiatives before support windows close. Security Operations Teams validate whether detected unsupported installations serve critical business functions or represent abandoned deployments that can be decommissioned.
Java Installation Details: Comprehensive configuration visibility supports both vulnerability validation and compliance verification activities. This chapter documents software installations identified through scanning operations, focusing on informational severity findings that indicate software presence. Risk Managers reference installation details when evaluating whether deployed software versions align with organizational standards and licensing agreements. Security Operations Teams utilize installation documentation to validate vulnerability scan accuracy and investigate false positive reports.
Hosts with the Most Java Installation Detections: Organizations must distinguish between vulnerability detections that indicate exploitable conditions and informational findings that document software presence without identifying security flaws. This chapter focuses on systems where scanning operations identify software installations rather than exploitable vulnerabilities. Risk Managers utilize installation detection data to understand software deployment patterns and licensing compliance rather than immediate security risks. Security Operations Teams reference installation detection chapters when conducting asset inventory audits and validating software management policies.
Top Java Exposures by Tenable VPR: Traditional severity scoring systems quantify potential impact if vulnerabilities experience successful exploitation but provide limited guidance about exploitation likelihood. This chapter applies Vulnerability Priority Rating (VPR) scores that incorporate threat intelligence, exploit availability, and attack pattern data. Risk Managers utilize VPR scores to differentiate between vulnerabilities that threat actors actively target and those that remain theoretical despite high CVSS ratings.
Hosts with the Most Java Vulnerabilities: Exposure concentration patterns indicate whether vulnerabilities distribute evenly across infrastructure or cluster on specific systems. This chapter identifies assets harboring disproportionate exposure quantities. Risk Managers investigate concentration patterns to determine whether clustering reflects intentional architectural decisions or unintended security gaps. Security Operations Teams prioritize hosts with extensive vulnerability counts because remediating a single high exposure system yields greater risk reduction than addressing multiple low-exposure assets.
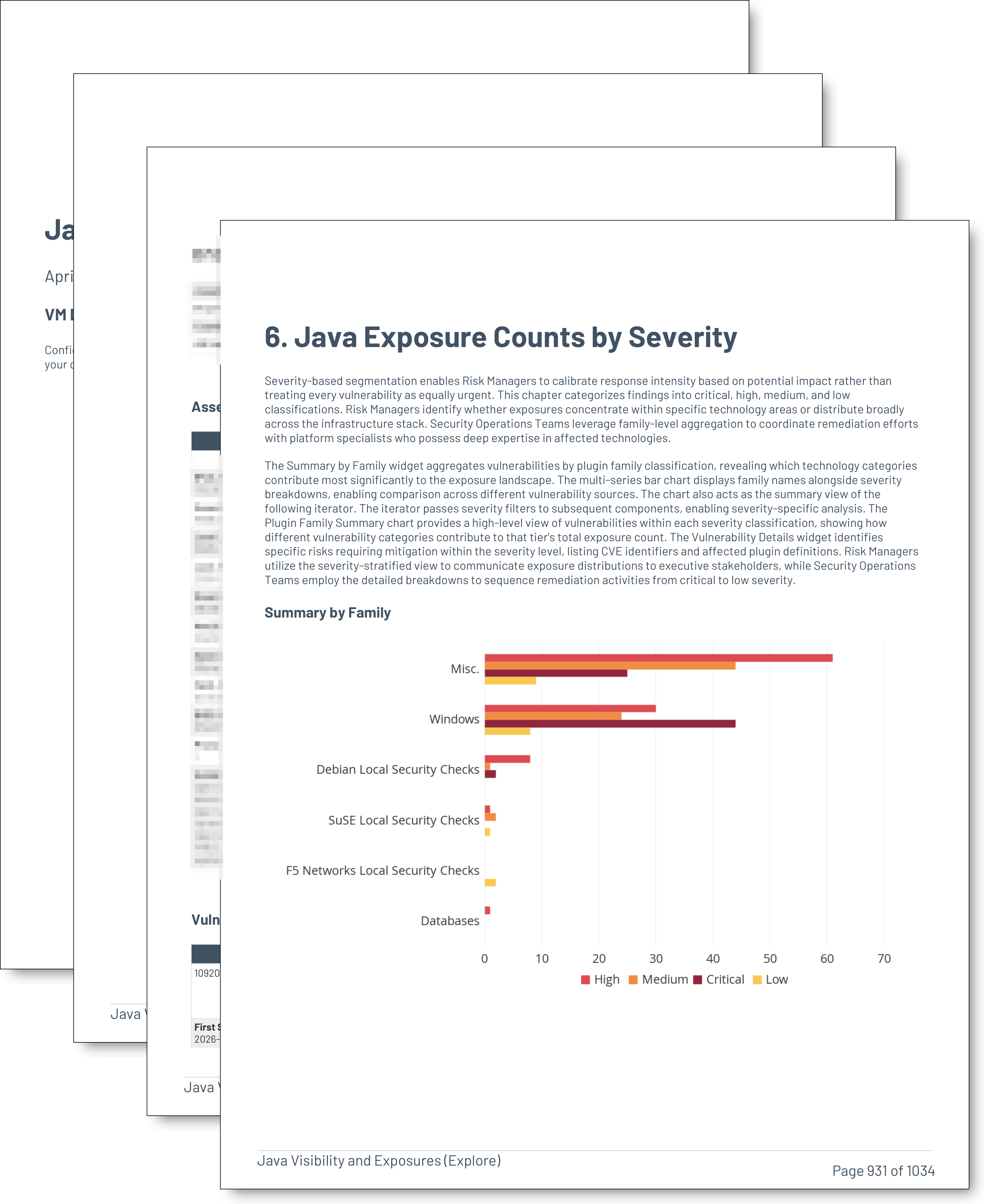
Java Exposure Counts by Severity: Severity-based segmentation enables Risk Managers to calibrate response intensity based on potential impact rather than treating every vulnerability as equally urgent. This chapter categorizes findings into critical, high, medium, and low classifications. Risk Managers identify whether exposures concentrate within specific technology areas or distribute broadly across the infrastructure stack. Security Operations Teams leverage family-level aggregation to coordinate remediation efforts with platform specialists who possess deep expertise in affected technologies.